Enhance Linux Authentication with Linux-PAM
Today, we will talk about the powerful framework in Linux used for authentication, which is Linux-PAM.
PAM or Pluggable Authentication Modules are the management layer that sits between Linux applications and the Linux native authentication system.
- 1 Linux-PAM benefit
- 2 Linux-PAM configuration
- 3 PAM services
- 4 Management groups
- 5 Control flags
- 6 Modules order
- 7 PAM modules
- 8 pam_succeed_if module
- 9 pam_nologin module
- 10 pam_access module
- 11 pam_deny module
- 12 pam_unix module
- 13 pam_localuser module
- 14 pam_mysql module
- 15 pam_cracklib module
- 16 pam_rootok module
- 17 pam_limits module
Linux-PAM benefit
There are many programs on your system that use PAM modules like su, passwd, ssh, login, and other services. We will discuss some of them.
PAM’s main focus is to authenticate your users.
Authentication in Linux is done by matching the encrypted password in /etc/shadow file with the entered one.
We have many services on our systems that require authentication like SSH, FTP, TELNET, IMAP, and many other services. So, we will have a lot of authentication files besides /etc/shadow file to maintain, and it could be a serious problem if there is any inconsistent data between these authentication files.
Here comes PAM. Linux-PAM offers a unified login system for your services.
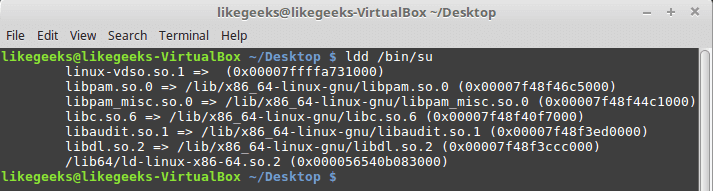
To check if your program uses Linux-PAM or not:
$ ldd /bin/su
You should see libpam.so library.
Linux-PAM configuration
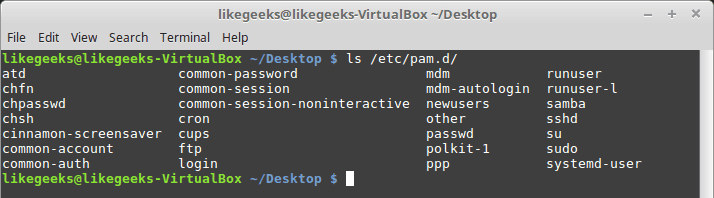
The configuration of Linux-PAM is in the directory /etc/pam.d/.
Some PAM modules require configuration files with the PAM configuration to operate. You can find the configuration files in /etc/security.
If you misconfigure PAM, this could lead to serious problems.
PAM services
The four types of PAM services:
- Authentication service modules.
- Account management modules.
- Session management modules.
- Password management modules.
Any application requires authentication can register with PAM using a service name.
You can list Linux services that use Linux-PAM.
$ ls /etc/pam.d/
If you open any service file, you will see that the file is divided into three columns. The first column is the management group, the second column is for control flags, and the third column is the module (so file) used.
$ cat /etc/pam.d/sshd
account required pam_nologin.so
The account is the management group, required is the control flag, and the used module is pam_nologin.so.
You may find a fourth column, which is for module parameters.
Management groups
There are four Management Groups you will see in PAM services files:
- Auth Group: it can validate users
- Account Group: controls the access to the service like how many times you should use this service.
- Session Group: responsible for the service environment.
- Password Group: for password updating.
Control flags
We have four control flags in services files:
- Requisite: the strongest flag. If the requisite not found or failed to load, it will stop loading other modules and return failure.
- Required: The same as requisite, but if the module failed to load for any reason, it continues loading other modules and returns failure at the end of execution.
- Sufficient: if the module return success, the processing of other modules no longer needed.
- Optional: In the case of failure, the stack of modules continues execution, and the return code is ignored.
Modules order
The order is important because each module depends on the previous module on the stack.
If you try a configuration like the following to log in:
auth required pam_unix.so auth optional pam_deny.so
That will work correctly, but what will happen if we change the order like this:
auth optional pam_deny.so auth required pam_unix.so
No one can log in, so the order matters.
PAM modules
There are PAM built-in modules on your system that you should know about, so you can use them perfectly.
pam_succeed_if module
This module allows access for the specified groups. You can validate user accounts like this:
auth required pam_succeed_if.so gid=1000,2000
The above line states that only users in the group whose ID 1000 or 2000 are allowed to log in.
You can use uid as the user id instead.
auth requisite pam_succeed_if.so uid >= 1000
In this example, any user id greater than or equal 1000 can log in.
You can also use it with ingroup parameter like this:
auth required pam_succeed_if.so user ingroup mygroup
Only people in the group named mygroup can log in.
pam_nologin module
This module allows root only to log in if the file is available.
/etc/nologin
auth required pam_nologin.so
You can modify the login service file with this line and create /etc/nologin file, so root only can log in.
And you can use it with auth, account management groups.
pam_access module
This module works like the pam_succeed_if module except the pam_access module checks logging from networked hosts, while the pam_succeed_if module doesn’t care.
account required pam_access.so accessfile=/etc/security/access.conf
You can type your rules in the file like this:
/etc/security/access.conf
+:mygroup -:ALL:ALL
The above rules state that only mygroup users are allowed to log in while others can’t.
Where plus sign means allow and minus sign means deny.
This module is used with auth, account, session, password management groups.
pam_deny module
You can use this module for restricting access. It will always return a non-OK.
You can use it at the end of your module stack to protect yourself from any misconfiguration.
If you use it at the beginning of the module stack, your service will be disabled:
auth required pam_deny.so auth required pam_unix.so
And you can use it with auth, account, session, password management groups.
pam_unix module
You can use this module to check the user’s credentials against /etc/shadow file.
auth required pam_unix.so
You will see this module used in many services in your system.
And you can use it with auth, session, password management groups.
pam_localuser module
You can use this module to check if the user is in /etc/passwd.
account sufficient pam_localuser.so
And you can use it with auth, session, password, account management groups.
pam_mysql module
Instead of checking the user’s credentials against/etc/shadow, you can use a MySQL database as a backend using the pam_mysql module.
You can use it like this:
auth sufficient pam_mysql.so user=myuser passwd=mypassword host=localhost db=mydb table=users usercolumn=username passwdcolumn=password
Here we validate the user with the parameters for pam_mysql.
You can install if it is not on your system like this:
$ yum install libpam-mysql
We use this module with auth, session, password, account management groups.
pam_cracklib module
Strong passwords are a must these days. This module ensures that you will use strong passwords.
password required pam_cracklib.so retry=4 minlen=12 difok=6
This example ensures that:
Password minimum length = 12
Four times to pick a strong password; otherwise, it will exit.
Your new password must have six new characters from the old password. You can use this module with the password management group.
pam_rootok module
This module checks if the user ID is 0, which means only root users can run this service.
auth sufficient pam_rootok.so
We use this module to ensure that a specific service is allowed for root users only, and you can use it with the auth management group.
pam_limits module
You can use this module to set limits on the system resources. It affects even root users.
The limits configuration is in the /etc/security/limits.d/ directory.
session required pam_limits.so
You can use this module to protect your system resources, and you can use it with the session management group.
The limits in /etc/security/limits.conf file could be hard or soft.
Hard: The user cannot change its value, but root can.
Soft: normal user can change it.
The limits could be fsize, cpu, nproc, nproc, data, and many other limits.
@mygroup hard nproc 50 myuser hard cpu 5000
The first limit for mygroup members, which sets the number of processes for each one of them to be 50.
The second limit for the user named myuser, which limits the CPU time to 5000 minutes.
You can edit any PAM service file in /etc/pam.d/ and use the module you want to protect your services the way you want.
I hope you find using Linux PAM modules easy and useful.
Thank you.
Mokhtar is the founder of LikeGeeks.com. He is a seasoned technologist and accomplished author, with expertise in Linux system administration and Python development. Since 2010, Mokhtar has built an impressive career, transitioning from system administration to Python development in 2015. His work spans large corporations to freelance clients around the globe. Alongside his technical work, Mokhtar has authored some insightful books in his field. Known for his innovative solutions, meticulous attention to detail, and high-quality work, Mokhtar continually seeks new challenges within the dynamic field of technology.

Hey there,
I am a newbie to Linux and I am having certain questions.
Actually I want to add face recognition as my authentication method(The code of which is in python.), And I am going to use the pam_python module which will let my python code communicate with pam module of Linux.
So the question is that where exactly I will have to add a file with *auth required pam_python.so /lib/security/..*.
And if the place to add this line is pam.d then in which file I will have to add this line.
If you mean adding the rules, then you can add it in /etc/pam.conf like this:
login auth requisite pam_python.so pam_accept.pyBut there is already a pam.d directory in my /etc directory. And there is a commented line in the pam.conf that this file(pam.conf) will be ignored if there is a pam.d directory in /etc.
Give it a try and use it and check the results.
Okay. Thank you so much.
You’re welcome! Thanks!
Hi,
very interesting article. I am wondering if PAM authentication can be used also on embedded Linux environment.
I’m trying to cross compile Linux-PAM for embedded, but in the resulting directory I couldn’t find any pam.d directory inside the etc folder. Also, pam.config is not present too.
Is it an expected behavior or I did something wrong during the cross-compilation?
I would have imagined finding a /etc/pam.d folder in which to add the services that use PAM.
Thank you a lot.
Hi Andrew,
Actually, I didn’t compile Linux-PAM for embedded systems before, but as long as you didn’t receive any errors, everything should be OK.
Regards,
Hi Mokhtar,
thank you for you answer. I think you’re right. Perhaps should I move all the compiled result on the target and create the /etc/pam.d folder by myself?
Thank you.
Go ahead and try.